Worm Virus Download

- Storm Worm Virus free download - Storm, Multi Virus Cleaner 2011, Symantec Virus Definitions & Security Updates (32-bit), and many more programs.
- 84,887 downloads Updated: December 19, 2011 Freeware. Review Free Download. Remove worm Remove trojan Remove virus Worm Trojan Virus Antivirus. Anti.worm was reviewed by Sorin.
- Worm:W32/Conficker.AL is a variant of Worm:W32/Downadup that can spread using three different methods and is capable of hiding its actions on the infected machine, as well as downloading files from remote sites.
Morris Worm source code disk at the Computer History Museum.
Spread of Conficker worm.
A computer worm is a standalone malwarecomputer program that replicates itself in order to spread to other computers. Often, it uses a computer network to spread itself. This is due to security shortcomings on the target computer. Unlike a computer virus, it does not need to attach itself to an existing program. Worms almost always cause at least some harm to the network, even if only by consuming bandwidth, whereas viruses almost always corrupt or modify files on a targeted computer.
Contents |
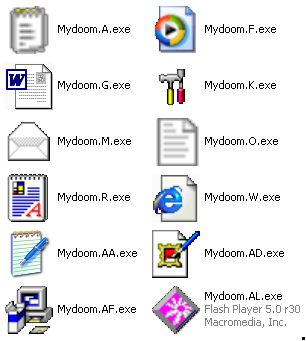
Download Virus Email Worm Win32 Mydoom.aa Password: downloadviruss.wordpress.com. Game counter strike point blank full version.
Payloads
Many worms that have been created are designed only to spread, and don’t attempt to change the systems they pass through. However, as the Morris worm and Mydoom showed, even these “payload free” worms can cause major disruption by increasing network traffic and other unintended effects. A “payload” is code in the worm designed to do more than spread the worm–it might delete files on a host system (e.g., the ExploreZip worm), encrypt files in a cryptoviral extortion attack, or send documents via e-mail. A very common payload for worms is to install a backdoor in the infected computer to allow the creation of a “zombie” computer under control of the worm author. Networks of such machines are often referred to as botnets and are very commonly used by spam senders for sending junk email or to cloak their website’s address.[1] Spammers are therefore thought to be a source of funding for the creation of such worms,[2][3] and the worm writers have been caught selling lists of IP addresses of infected machines.[4] Others try to blackmail companies with threatened DoS attacks.[5]
Backdoors can be exploited by other malware, including worms. Examples include Doomjuice, which spreads better using the backdoor opened by Mydoom, and at least one instance of malware taking advantage of the rootkit and backdoor installed by the Sony/BMGDRM software utilized by millions of music CDs prior to late 2005.[6][dubious – discuss]
Worms with good intent
Beginning with the very first research into worms at Xerox PARC, there have been attempts to create useful worms. The Nachi family of worms, for example, tried to download and install patches from Microsoft’s website to fix vulnerabilities in the host system–by exploiting those same vulnerabilities. In practice, although this may have made these systems more secure, it generated considerable network traffic, rebooted the machine in the course of patching it, and did its work without the consent of the computer’s owner or user.
Some worms, such as XSS worms, have been written for research to determine the factors of how worms spread, such as social activity and change in user behavior, while other worms are little more than a prank, such as one that sends the popular image macro of an owl with the phrase “O RLY?” to a print queue in the infected computer. Another study proposed what seems to be the first computer worm that operates on the second layer of the OSI model (Data link Layer), it utilizes topology information such as Content-addressable memory (CAM) tables and Spanning Tree information stored in switches to propagate and probe for vulnerable nodes until the enterprise network is covered.[7]
Most security experts regard all worms as malware, whatever their payload or their writers’ intentions.
Protecting against dangerous computer worms
Worms spread by exploiting vulnerabilities in operating systems. Vendors with security problems supply regular security updates[8] (see “Patch Tuesday“), and if these are installed to a machine then the majority of worms are unable to spread to it. If a vulnerability is disclosed before the security patch released by the vendor, a zero-day attack is possible.
Users need to be wary of opening unexpected email,[9] and should not run attached files or programs, or visit web sites that are linked to such emails. However, as with the ILOVEYOU worm, and with the increased growth and efficiency of phishing attacks, it remains possible to trick the end-user into running a malicious code.
Anti-virus and anti-spyware software are helpful, but must be kept up-to-date with new pattern files at least every few days. The use of a firewall is also recommended.
In the April–June, 2008, issue of IEEE Transactions on Dependable and Secure Computing, computer scientists describe a potential new way to combat internet worms. The researchers discovered how to contain the kind of worm that scans the Internet randomly, looking for vulnerable hosts to infect. They found that the key is for software to monitor the number of scans that machines on a network sends out. When a machine starts sending out too many scans, it is a sign that it has been infected, allowing administrators to take it off line and check it for viruses.[10][11] In addition, machine learning techniques can be used to detect new worms, by analyzing the behavior of the suspected computer.[12]
Mitigation techniques
- ACLs in routers and switches
- TCP Wrapper/libwrap enabled network service daemons
History
The actual term “worm”‘ was first used in John Brunner‘s 1975 novel, The Shockwave Rider. In that novel, Nichlas Haflinger designs and sets off a data-gathering worm in an act of revenge against the powerful men who run a national electronic information web that induces mass conformity. “You have the biggest-ever worm loose in the net, and it automatically sabotages any attempt to monitor it… There’s never been a worm with that tough a head or that long a tail!”[13]
On November 2, 1988, Robert Tappan Morris, a Cornell University computer science graduate student, unleashed what became known as the Morris worm, disrupting an estimated 10% of the computers then on the Internet[14][15] and prompting the formation of the CERT Coordination Center[16] and Phage mailing list.[17] Morris himself became the first person tried and convicted under the 1986 Computer Fraud and Abuse Act.[18]
Reference
wikipedia
Though viruses, trojans, worms, spyware, rootkits etc all types of computer and mobile malware are hated by all of us, still they are crying needed for some persons. The term malware is used to mean malicious programs or softwares which are made to do illegal or malicious job on our computer or PDA system. But you may have question, “What types of people need virus samples?”
The persons whose need virus samples:
- Malware Authors: Malware authors are the main baby of all virus , trojan, worm world. They are the first creator of viruses.
| malware author |
- Hackers : Hackers are the number one persons whose are mostly interact with virus. They are engaged in making hack tools, spyware, rootkits to accomplish their hacking and cracking activities.
| hacker |
- AntiVirus and Security Tool Owners : All antivirus and security software owners must need virus samples. Because all anti-virus, anti-spyware etc work with own malware database. Malware or virus databases are application database where malware definitions and identities are recorded. A virus sample is needed to make its definition.
- Ethical Hackers : Ethical hackers are actually white hat hackers those research and works for cyber security. Generally these hackers work in individual company and try to make their company’s computer and online systems more secured so that other black hat hackers will not able to hack their company’s system.
| ethical hackers |
- Virus Lovers : Virus lovers are not VIP person as above. These persons are actually very curious about computer viruses. They try to know how they work. Some of them become expert about viruses by researching with them. So they acquire enough knowledge and experience to protect themselves from virus.
- Computer and Technology Students : Computer students from any computer and technology related subject need virus sample to experiment with them.
| computer students |
- Others : Other persons my indicate computer teachers, IT consultants, IT Journalists, Bloggers etc also computer virus sample.
/izotope-rx-7-mac-cracked.html. Now you understood why virus samples are useful. But you should care about viruses even if you don’t have above causes. There is a quotation by the author of www.vxheaven.com is “Viruses don’t harm, Ignorance does!” This means that viruses cannot harm you if you know about them. But if you always ignore them, you will have little knowledge about them. So they will able infect your system!
| www.vxheaven.com home page |
| www.vxheavens.com/vl.php virus collection |
Features of vxheaven :
- Free virus collection for download.
- All viruses are categorized with their types such as Trojans, spyware, Worms, Rootkits, Hoaxes, Hack Tools, Backdoors, Exploits etc.
- All viruses are divided with their OS(Operating System) support such as Microsoft Windows(XP, VIsta, 7), DOS, Apple Mac OS X, Linux(Ubuntu, Fedora etc), Java(J2ME, J2SE etc), HTML, BSD, Mobile OS(Symbian, WinCE, Windows Mobile, Android, Palm, iOS, iPhone, Blacberry etc.
- Virus serving and protecting utilities.
- Virus creating utilities and generator.
- Virus news updates and blogs, articles, books etc.
- Forum for discussion.
- Virus sources and polymorphic engines.
- Virus writing writing tutorials.
- Detailed information about every virus.
2.offensivecomputing.net :Offensivecomputing.net is another virus serving and blogging site. This site is intended to provide discussion environment by blog and virus samples so that people can share information about viruses. The viruses here are not uploaded by the owner of the site. All viruses are uploads by general people.
| virus details at offensivecomputing.net |
Features of vxheavens :
- Any one can upload virus here with simple uploader.
- Registered users can search and download viruses in zip package.
- Viruses are protected with the password “infected“. So extract the virus executable(exe, msi, pif, bat etc) files from zip package using the password infected.
- With free blog, users can share any information or request withe other people.
- With automatic online antivirus scanner, users can see the alias name of a virus.
3. openrce.org :Openrce.org is a site of open source viruses. Here you can get various types of viruses, rootkits, hackingtools with their source code.
| www.openre.org download page |
4.exploit-db.com : Exploit-db.com is a site of hackers where hackers and computer vulnerability researchers share there exploit tools and make discussion on them. Here you can get exploits for Linux, Windows, Mac OS X, ASP, PHP, BSD etc.
| www.exploit-db.com home page |
5. inj3ct0r.com : Inj3ct0r.com is the site of expert exploit hackers from where you can get many hacking exploits for windows, MAC OS X, Perl, PHP, Win32 etc.
| www.inj3ct0r.com home page |
https://trainintensive.weebly.com/blog/x-plane-mac-free-download. There are many other sites for open virus collection. You can inform me if you know more sites.
Trojan Virus Download Worm
Warning: TechGainer.com is not responsible for any damage of your system caused by virus resources from here.